A supply chain attack, also called a third-party attack, occurs when a bad actor infiltrates your system through an outside provider with access to your systems and data. This type of attack has dramatically changed the attack surface of the typical enterprise, as more suppliers and service providers are touching sensitive data than ever before.
Software supply chain attacks inject malicious code into an application in order to infect all users of an app, while hardware supply chain attacks compromise physical components for the same purpose.
Historically, supply chain attacks have referred to attacks against trusted relationships, in which an unsecure supplier in a chain is attacked in order to gain access to their larger trading partners. This is what happened in the 2013 attack against Target (NYSE:TGT), where the threat actor gained access to an HVAC contractor in order to enter Target’s systems.
However, today the greater concern is a software supply chain attack. Software supply chains are particularly vulnerable because modern software is not written from scratch: rather, it involves many off-the-shelf components, such as third-party APIs, open-source code and proprietary code from software vendors.
Today, the average software project has 203 dependencies. If a popular app includes one compromised dependency, EVERY BUSINESS that downloads from the vendor is compromised as well, so the number of victims can grow exponentially.
Supply Chain Attack Statistics:
Below are some 2021 statistics from CrowdStrike’s Global Security Attitude Survey:
- 84% believe that software supply chain attacks could become one of the biggest cyber threats to organizations like theirs within the next three years
- Only 36% have vetted all new and existing suppliers for security purposes in the last 12 months
- 45% of respondents’ organizations experienced at least one software supply chain attack in the last 12 months, compared to 32% in 2018
- 59% of organizations that suffered their first software supply chain attack did not have a response strategy
Attacks on the Rise
Supply chain attacks have increased exponentially, partly because as enterprises have become better at hardening their traditional attack surface environments, malicious attackers have turned to alternative targets and have found more creative ways to make their efforts difficult to detect.
Below are the types of supply chain attacks:
As occurred with the Solar Winds (https://www.cisecurity.org/solarwinds) attack, upstream server attacks are the most common type of attack. In this scenario, a malicious actor infects a system that is “upstream” of users, such as through a malicious update, which then infects all the users “downstream” who download it.
Midstream attacks target intermediary elements such as software development tools.
Dependency confusion attacks exploit private internally created software dependencies by registering a dependency with the same name but with a higher version number on a public repository. The false dependency is then likely to be pulled into the software build instead of the correct dependency.
Stolen SSL and code-signing certificate attacks compromise the private keys used to authenticate users of secure websites and cloud services. Stuxnet falls into this category.
CI/CD infrastructure attacks introduce malware into the development automation infrastructure, such as by cloning legitimate GitHub repositories.
Open-source software attacks introduce code into builds that propagate downstream to those who use the build.
Examples of Supply Chain Attacks
The SolarWinds attack is the supply chain attack that everyone is most familiar with. This was a complex attack that injected malicious code into the software’s build cycle and initially infected about 18,000 customers downstream, including major firms and government agencies that were secured by the strongest cybersecurity tools and services available today.
Another sophisticated supply chain attack targeted the ASUS Live Utility https://www.cnet.com/tech/computing/asus-pushes-patch-after-hackers-used-updates-to-send-malware a software utility that is pre-installed on ASUS systems and automatically updates a computer’s BIOS, drivers, applications, and other components. Over 57,000 users are known to have downloaded and installed the compromised utility. This was a targeted attack aimed at a group of users with specific MAC addresses.
A popular open-source JavaScript tool was the target of an attack aimed at Linux and macOS operating systems. The attack used a technique called brandjacking, which tricks users into downloading malicious code. There are many other attacks of this type that are missed. In 2020, at least 26 open-source projects were targeted in supply chain attacks.
How Do You Prevent and Detect a Supply Chain Attack?
Supply chain attacks are increasingly becoming a business-critical issue that’s impacting crucial relationships with partners and suppliers. Supply chain attacks are hard to detect. And just because a software product was validated in the past doesn’t mean that software is secure today.
Along with rigorously assessing the vendors they use, organizations need to mitigate the supply chain risks that are making them vulnerable to attack. This requires employing effective prevention, detection, and response technologies.
Recommendations for Improving Supply Chain Security
The following are some recommendations for how organizations can improve their supply chain security and avoid becoming a victim:
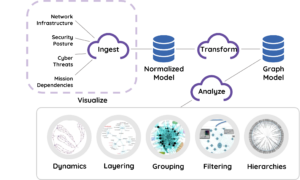
- Employ solutions that include behavioral-based attack detection, such a TruContext with the MITRE ATT&CK framework. The sophisticated nature of supply chain attacks requires organizations to employ graph analysis, combined with the power of behavioral-based analysis such as indicators of attack (IOAs). Mitigating the risks incurred “when good programs go bad” requires technologies such as TruContext’s visualization and machine learning (ML) that can detect patterns in hundreds, thousands or even millions of attacks per day — a feat that can’t be accomplished with human insight alone.
- Get ahead of future supply chain attacks with threat intelligence. Threat intelligence will tell you when new supply chain attacks emerge and provide you with all the information you need to understand the attack and proactively defend against it. TruContext works with CrowdStrike data that combines malware analysis, and malware search and threat intelligence to deliver context-rich information that enables predictive security.